100G data center network upgrade solution - 100G OCP3.0 Server NIC
LR-LINK Flagship Series | More Stable and Compatible
The Most Significant Events in 2023 | LR-LINK
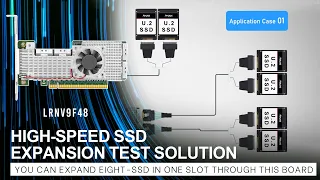
High-speed SSD Expansion Test Solution - SSD Testing
LR-LINK Company Introduction
JUMBO FRAME GRABBER: Designed for 5GigE industrial cameras (LRES2055PT-POE)